Facial Access Controls
Facial Access Controls, also known as Facial Recognition Access Systems, are advanced security solutions that use facial recognition technology to grant or deny access to secured areas or devices. These systems work by capturing and analyzing an individual’s unique facial features, such as the geometry of their face, to verify their identity …..

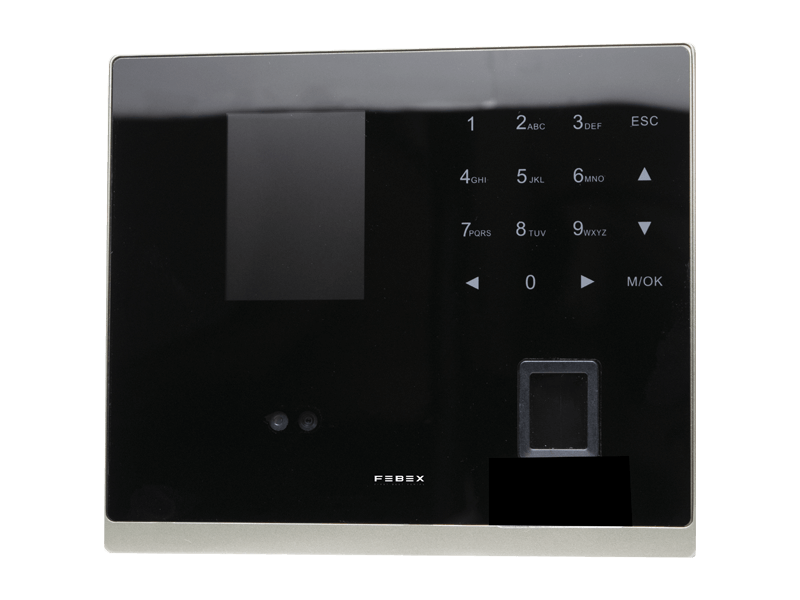
Fingerprint Access Controls
Fingerprint Access Controls, often referred to as Fingerprint Recognition Access Systems, are cutting-edge security solutions designed to regulate access to restricted areas or devices. These systems employ biometric technology to identify individuals based on their unique fingerprint patterns …..

RFID Access Controls
RFID (Radio-Frequency Identification) Access Controls are sophisticated security systems that utilize RFID technology to manage and regulate access to various areas, assets, or devices. These systems work by utilizing RFID tags or cards that contain unique identification information …..

Access Control Panels
Access Control Panels are the central nerve centers of advanced security systems. These panels are specialized electronic devices that manage and control access to secured areas or assets within a facility. They serve as the brains behind access control systems, orchestrating the authentication and authorization processes …..
Maximizing Security with Access Control Systems: supplier and manfacturere
Access control systems have become a cornerstone of modern security strategies, offering a robust suite of advantages for safeguarding both physical and digital assets. These systems are designed to regulate and manage access, providing a multitude of benefits that contribute to heightened security. In this article, we’ll delve into the various benefits of access control systems while shedding light on the two main types: physical and logical access control.
Benefits of Access Control Systems
- Enhanced Security: Access control systems significantly bolster security by preventing unauthorized access to sensitive areas. The implementation of these systems ensures that only authorized individuals gain entry, thereby reducing the risk of theft, vandalism, or data breaches.
- Simplified Management: Access control devices streamline the management of access permissions. Administrators can effortlessly control who has access to specific resources, granting or revoking permissions as required. This simplifies the process of granting and managing access.
- Real-time Monitoring: Many access control systems offer real-time activity tracking, allowing organizations to monitor access to specific areas or digital assets at any given time. This real-time monitoring not only enhances security but also promotes accountability.
- Elimination of Traditional Keys: Access control systems eliminate the need for physical keys, which can be easily lost or stolen. This reduction in the risk of unauthorized access due to misplaced keys enhances overall security.
- Customizable Access Times: Organizations can establish specific access times and restrictions, ensuring that access is granted only when necessary. This level of control further reinforces security measures.
- Enhanced Employee Freedom: Access control systems grant authorized employees the freedom to move about while maintaining a secure environment. This balance between convenience and safety is a hallmark of access control systems.
- Prevention of Disruptions: Access control devices can effectively prevent disruptions to business operations. By regulating access to critical areas, they ensure business continuity.
In conclusion, access control devices play an indispensable role in maintaining security and control over both physical and digital assets. Their ability to restrict access to authorized individuals, provide real-time monitoring, and simplify access management is essential for organizations seeking to protect their resources from unauthorized access and security threats.
Types of Access Control Systems
Now, let’s explore the two main types of access control systems: physical and logical access control.
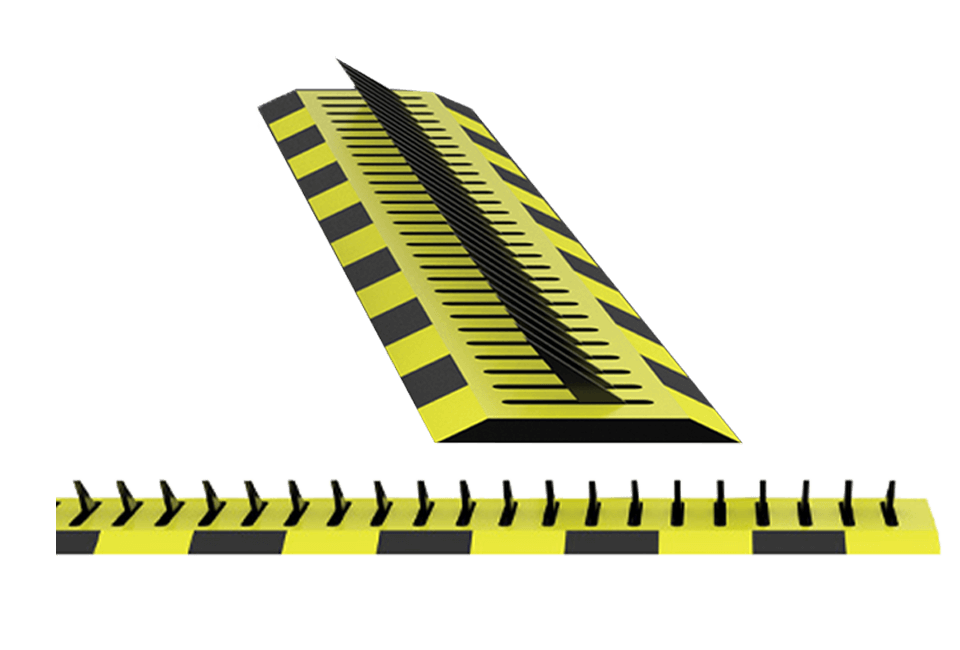
Physical Access Control Systems
These systems are designed to restrict access to physical locations, including buildings, rooms, and equipment. Various technologies are used for physical access control, such as:
- Key card systems: Users swipe a key card through a reader to gain access to a secure area.
- Biometric scanners: Biometric data, like fingerprints or facial recognition, is used for user identification and authentication.
- PIN pad systems: Users enter a PIN code into a keypad to gain access to a secure area.
Logical Access Control Systems
These systems focus on restricting access to computer systems and networks. They employ different authentication methods, including:
- Password systems: Users enter a password to access a computer system or network.
- Two-factor authentication (2FA): Users must provide two different factors, such as a password and a code from their phone, to log in.
- Multi-factor authentication (MFA): Users are required to provide three or more different factors, such as a password, a phone-generated code, and a fingerprint scan, for authentication.
Access control security systems are instrumental in protecting people, property, and information from unauthorized access. They serve as a bulwark against theft, espionage, and sabotage, ensuring the safety and security of both physical and digital assets.